Docker Image Scan results for centos/httpd
Scan performed at 2022-12-12 15:23:07 using the CoGuard CLI
Summary
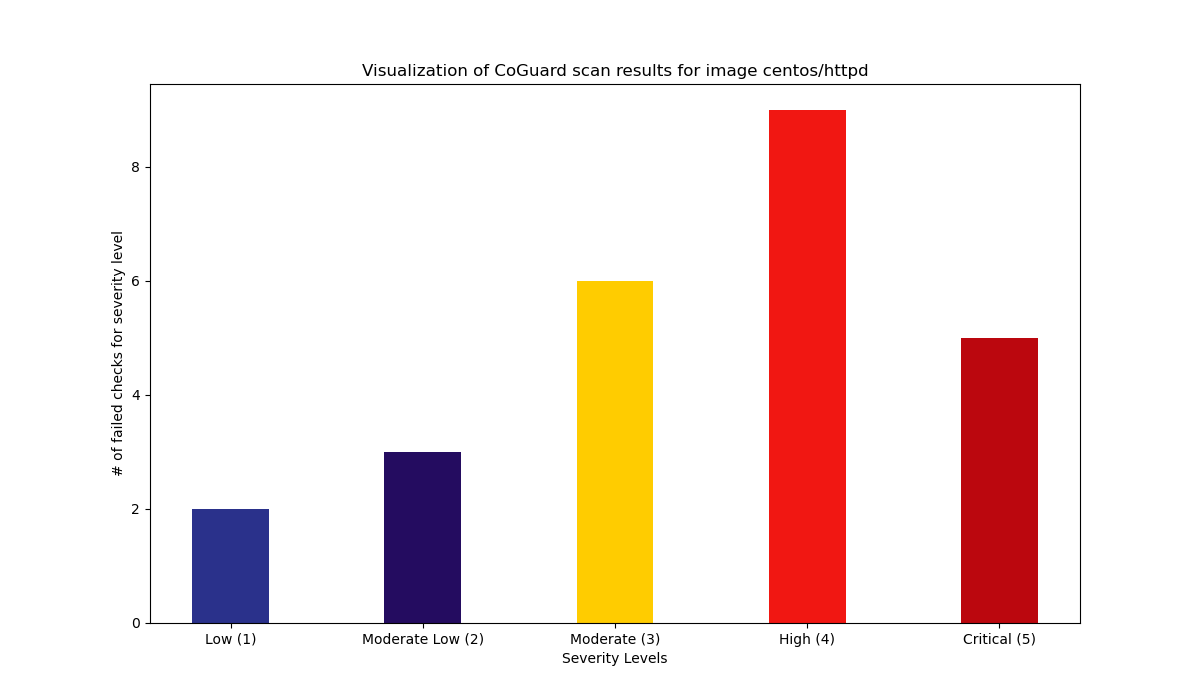
25 Total failed checks.
14 High / 6 Medium / 5 Low.
Details
| Rule identifier | Severity | Documentation |
|---|---|---|
| apache_deny_root_directory | 5 | Ensure that the root directory access is specifically denied. Otherwise, it is possible that an attacker can gain access to files through root directory mapping. Remediation: Create a Source:https://httpd.apache.org/docs/2.4/mod/core.html#directory |
| apache_root_directory_options_none | 5 | With the options directive, one can allow scripts to be executed, follow symlinks, do content negotiation, etc. In the root directory, the Options directive should always be set to None. Remediation: Create a Source:https://httpd.apache.org/docs/2.4/mod/core.html#directory |
| apache_enable_ssl | 5 | We should never have any communication done using unencrypted channels. This check tests if the mod_ssl.so module is loaded and that SSLProtocol is set, together with a proper SSL certificate file and a key file. Remediation: Load the mod_ssl.so modules, and set the SSLCertificateFile and SSLCertificateKeyFile keys to the paths of the respective certificate and key file. |
| apache_load_logging_module | 5 | Logging is important to monitor the activity on the server and detect anomalies. Remediation: Load the module mod_log_config module in the configurationSource: https://httpd.apache.org/docs/2.4/mod/mod_log_config.html |
| apache_load_security_module | 5 | ModSecurity is a module that acts as a web application firewall for monitoring, logging, and access control. It should always be loaded and configured Remediation steps: Load the module by adding LoadModule security2_module modules/mod_security2.soSource: https://www.modsecurity.org/download.html |
| apache_restrict_access_ht_files | 4 | There are special reserved files called .htaccess, .htgroup and .htpasswd. While it is not recommended to use them, it is also important to ensure that, if they are being used, access to them is restricted. Remediation: Add the directive Source:https://httpd.apache.org/docs/2.4/mod/core.html#filesmatch |
| dockerfile_last_user_should_be_non_root | 4 | When creating a Docker container, it is possible to set the user who is actually running the application and any command on the container. It is important to specifically use the USER directive in any Dockerfile to ensure that the user is not root and has unnecessary privileges. Remediation: Have at least one USER directive in your Dockerfile, and the last user directive should not reference the root user or root group. Source: https://docs.docker.com/engine/reference/builder/#user |
| apache_turn_trace_off | 4 | It is considered best practice to have tracing disabled for Apache HTTP servers. Remediation: Set TraceEnable to off in your configurationSource: https://owasp.org/www-community/attacks/Cross_Site_Tracing |
| apache_content_security_policy_set | 4 | One of the most effective techniques to prevent cross site scripting attacks is to control where the content is served from. This can be achieved by setting specific policies in the Content-Security-Policy header. Remediation: The value of that header is completely up to the specific web service. In order to pass this check, the httpd.conf needs to contain a line of the form Header always append Content-Security-Policy <YOUR-CONTENT>Source: https://wiki.owasp.org/index.php/OWASP_Secure_Headers_Project#csp |
| apache_x_xss_protection_set | 4 | There is an HTTP response header that stops pages from loading in modern browsers when reflected cross site scripting attacks are detected. Remediation: Apache can automatically set this header for every response by setting Header always append X-XSS-Protection "1; mode=block"Source: https://wiki.owasp.org/index.php/OWASP_Secure_Headers_Project#xxxsp |
| apache_hsts_header_set | 4 | There is an HTTP response header that instructs the browser to only communicate with the website using HTTPS, the so called HSTS header. This one should be enabled. Remediation: Apache can automatically set this header for every response by setting `Header always append Strict-Transport-Security "max-age: Source: https://wiki.owasp.org/index.php/OWASP_Secure_Headers_Project#hsts |
| apache_x_content_type_header_set | 4 | There is an HTTP response header that disables the functionality of the browser to detect a content type automatically, which poses an attack vector. Remediation: Apache can automatically set this header for every response by setting Header always append X-Content-Type-Options "nosniff"Source: https://wiki.owasp.org/index.php/OWASP_Secure_Headers_Project#xcto |
| apache_x_frame_options_same_origin | 4 | There is an HTTP response header that makes it harder to do clickjacking. Apache can automatically set this header for every response by setting Header always append X-Frame-Options SAMEORIGINSource: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options |
| apache_run_as_separate_user | 4 | Apache should not be run as root. In fact, it is best to configure the user it is run as. Remediation: Set the User and Group directives to any user but root.Source: https://httpd.apache.org/docs/2.4/mod/mod_unixd.html |
| apache_no_directory_listing | 3 | When a user puts in a URL to a directory, the contents should not be listed. This may reveal files which the hoster does not want the user to know about. Remediation: In each Source: http://httpd.apache.org/docs/current/mod/core.html#directory |
| dockerfile_create_volume_for_var_log | 3 | In linux systems, important operating system logs are stored in the /var/log subfolder. This folder should always be made available to the host through a volume, so that log tracking and log analysis systems can capture them. Remediation: In every Dockerfile, there should be a VOLUME directive which has /var/log as an argument.Source: https://docs.docker.com/engine/reference/builder/ |
| apache_restrict_ssl_protocol | 3 | SSL 2.0, 3.0, TLS 1, 1.1 have reportedly several crytographic flaws. Hence, only TLS 1.2 should be used Remediation: Set SSLProtocol to -ALL +TLSv1.2 |
| apache_deny_anything_older_than_http_1_1 | 3 | Many malicious programs will try to send arbitrary requests to your Apache web server. It is important to only allow HTTP 1.1 requests, since support for older versions is obsolete. Remediation: Use the Rewrite engine module of Apache to filter out requests. Add the following lines: RewriteEngine On RewriteCond %{THE_REQUEST} !HTTP/1.1$ RewriteRule .* - [F] Source:http://httpd.apache.org/docs/current/mod/mod_rewrite.html |
| apache_server_tokens_off | 3 | Even when a user gets to an error page, there should never be more information than necessary displayed on the page. By not knowing the specific Apache HTTPd version, an attacker cannot match known issues to a certain attack. Remediation: Set ServerTokens to Prod or ProductOnly in your configuration.Source: https://httpd.apache.org/docs/2.4/mod/core.html#servertokens |
| apache_do_not_allow_override | 3 | The use of .htaccess files introduces the risk of unintentional configuration overrides. In newer versions of Apache, this is disabled by default. It is best to set these specifically to ensure it is really off. Remediation: In every Source: https://httpd.apache.org/docs/2.4/mod/core.html#directory |
| dockerfile_only_one_cmd_instruction | 2 | The CMD directive specifies the final command that is executed when running the container. This should be unique. Remediation: Ensure that there is at most one CMD directive in the Dockerfile. |
| dockerfile_container_healthcheck_parameter | 2 | Dockerfiles have an instruction called HEALTHCHECK. It enables a user to define a command to figure out if the program(s) running inside the container are working properly. It is generally advisable to have healthchecks in place to assist monitoring of running containers. Remediation: Have at least one HEALTHCHECK instruction in your Dockerfile.Source: https://docs.docker.com/engine/reference/builder/#healthcheck |
| apache_set_directory_options_none | 2 | It is recommended to keep the Options for Remediation: In every Options to be none.Source: https://httpd.apache.org/docs/2.4/mod/core.html#directory |
| dockerfile_do_not_use_maintainer | 1 | Dockerfiles allow for a specification of a MAINTAINER. This directive is deprecated, and should generally be replaced with the LABEL directive. Remediation: Remove any MAINTAINER directive in your Dockerfile and replace it with LABEL.Source: https://docs.docker.com/engine/reference/builder/#maintainer-deprecated |
| dockerfile_do_not_use_add | 1 | Dockerfiles have two directives that allow you to add files from the machine where you build the image into the image, namely COPY and ADD. Both are technically similar, but ADD also has side-effects like automated decompression of archives. It is generally recommended to only use COPY Remediation: Remove any ADD directive in your dockerfile and replace it with COPY.Source: https://docs.docker.com/engine/reference/builder/#copy |
Scan performed at 2022-12-12 15:23:07 using the CoGuard CLI