Docker Image Scan results for cimg/postgres
Scan performed at 2022-12-12 15:23:07 using the CoGuard CLI
Summary
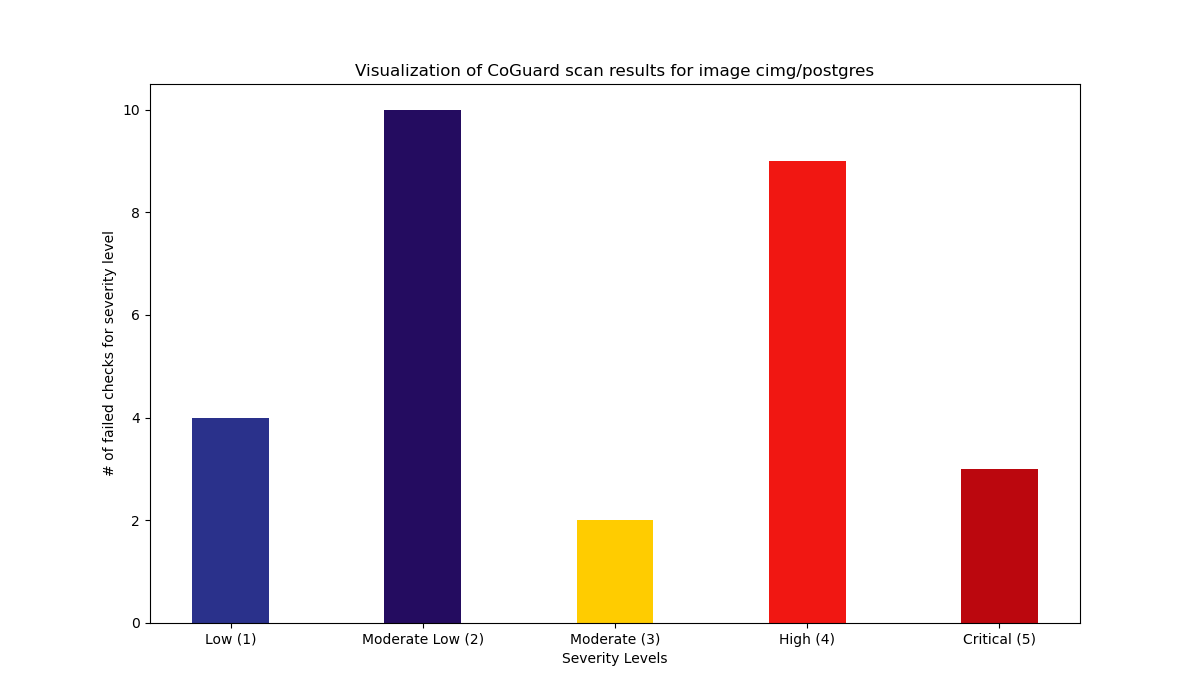
28 Total failed checks.
12 High / 2 Medium / 14 Low.
Details
| Rule identifier | Severity | Documentation |
|---|---|---|
| postgres_enable_ssl_traffic | 5 | The communication to the database should always be encrypted. Remediation: Set the ssl directive to on.Source: https://www.postgresql.org/docs/current/ssl-tcp.html |
| mysql_ensure_modern_tls | 5 | It is important to only support modern, i.e. currently deemed secure, TLS versions. Remediation: Set tls_version to TLSv1.2,TLSv1.3Source: https://dev.mysql.com/doc/refman/8.0/en/server-system-variables.html#sysvar_tls_version |
| mysql_have_ssl | 5 | It is important to enforce encrypted traffic to the MySQL server, i.e. use SSL certificates. Remediation: In the configuration, under [mysqld], set the variables ssl_cert and ssl_key to the paths to your certificate and keyfile, and set require_secure_transport to ON.Source: https://dev.mysql.com/doc/refman/5.7/en/using-encrypted-connections.html |
| postgres_enable_archive_mode | 4 | In order to perform point in time recovery, the archive mode in Postgres needs to be set to be on. Remediation: Set the directive archive_mode to on.Source: https://wiki.postgresql.org/wiki/Simple_Configuration_Recommendation |
| mysql_ensure_password_strength | 4 | MySql has configuration parameters that allow for setting policies for password strengths. This check ensures that the respective parameters are set to appropriate values. Remediation: The following conditions must hold for this check to pass: - validate_password_length > 10 - validate_password_mixed_case_count > 0 - validate_password_number_count > 0 - validate_password_special_char_count >0 - validate_password.policy >1- plugin_load must contain validate_password.so- validate-password must be FORCE_PLUS_PERMANENT |
| dockerfile_last_user_should_be_non_root | 4 | When creating a Docker container, it is possible to set the user who is actually running the application and any command on the container. It is important to specifically use the USER directive in any Dockerfile to ensure that the user is not root and has unnecessary privileges. Remediation: Have at least one USER directive in your Dockerfile, and the last user directive should not reference the root user or root group. Source: https://docs.docker.com/engine/reference/builder/#user |
| mysql_default_password_lifetime_bounded | 4 | MySql, by default, has no password expiration. It is recommended to renew passwords on a compliance based schedule. Remediation: Set the parameter default_password_lifetime to any value other than 0.Source: https://dev.mysql.com/doc/refman/8.0/en/server-system-variables.html#sysvar_default_password_lifetime |
| mysql_sql_mode_no_auto_create_user | 4 | MySql has a SQL interpreter setting that enables the behavior that a user is automatically created if authentication information is not provided, hence allowing to accidentally create a user without a password. Add NO_AUTO_CREATE_USER to the sql_mode list.Source: https://dev.mysql.com/doc/refman/5.7/en/server-options.html#option_mysqld_sql-mode |
| mysql_add_strict_all_tables_to_sql_mode | 4 | MySql has different modes for its SQL engine. It is important to have MySql behave as strictly as possible to avoid an additional attack surface. Remediation: Have STRICT_ALL_TABLES in the sql_mode list under mysqld.Source: https://dev.mysql.com/doc/refman/8.0/en/server-options.html#option_mysqld_sql-mode |
| mysql_prevent_local_file_load | 4 | MySql allows to load local files via LOAD DATA INFILE or SELECT local_file. Unless explicityly needed, this setting should generally be turned off.Remediation: Set the key local_infile to 0 in the mysqld section.Source: https://dev.mysql.com/doc/refman/8.0/en/mysql-command-options.html#option_mysql_local-infile |
| mysql_log_errors | 4 | By default, MySql logs errors to the console. These logs contain vital information for debugging and anomaly detection. It is important to set the setting to write these logs into a file, so that log-analyzers can include the results. Remediation: Set the parameter log_error in your configuration to a path of your choice. Also ensure that MySql is not started with the --console parameter, as it overwrites this setting in newer versions.Source: https://dev.mysql.com/doc/refman/5.7/en/error-log.html |
| mysql_secure_file_priv_set | 4 | Although there is a different check to ensure that local files are not loaded, it may be sometimes desiarable. If this is the case, then one should at least restrict the directory where the files can come from. This can be done by setting the secure_file_priv variable.Remediation: If local-infile is set to 1 (default), then secure_file_priv needs to be set to a specific directory.Source: https://dev.mysql.com/doc/refman/8.0/en/server-system-variables.html#sysvar_secure_file_priv |
| dockerfile_create_volume_for_var_log | 3 | In linux systems, important operating system logs are stored in the /var/log subfolder. This folder should always be made available to the host through a volume, so that log tracking and log analysis systems can capture them. Remediation: In every Dockerfile, there should be a VOLUME directive which has /var/log as an argument.Source: https://docs.docker.com/engine/reference/builder/ |
| mysql_enable_general_log | 3 | MySQL has by default general log information disabled, which includes important information such as connection information. This general logging mechanism should be enabled. Remediation: Set the parameter general_log to ON in your configuration.Source: https://dev.mysql.com/doc/refman/8.0/en/server-system-variables.html#sysvar_general_log |
| postgres_enable_logging_connections | 2 | Postgresql offers a mechanism to log connections to the database. This is recommended to be turned on, as it enables the system administrator to analyze these logs and detect anomalies. Remediation: Set the directive log_connections to on.Source: https://wiki.postgresql.org/wiki/Simple_Configuration_Recommendation |
| postgres_enable_logging_disconnections | 2 | Postgresql offers a mechanism to log ends of sessions, including the duration of sessions. This is recommended to be turned on, as it enables the system administrator to analyze these logs and detect anomalies. Remediation: Set log_disconnections to onSource: https://www.postgresql.org/docs/9.1/runtime-config-logging.html |
| dockerfile_only_one_cmd_instruction | 2 | The CMD directive specifies the final command that is executed when running the container. This should be unique. Remediation: Ensure that there is at most one CMD directive in the Dockerfile. |
| postgres_ensure_log_directory_is_set | 2 | Postgres allows you to set your own log directory, which in turn ensures that the user as which Postgresql is run is allowed to write into that directory. It is recommended to set this directory specifically. Remediation: Set log_directory to a value of your choice.Source: https://www.postgresql.org/docs/10/runtime-config-logging.html |
| postgres_ensure_log_rotation_size_not_disabled | 2 | Log file rotation by by size is part of logging best practices. It is important to have a value set there that follows your companie's policies Remediation: Set the parameter log_rotation_size to any value other than 0Source: https://www.postgresql.org/docs/10/runtime-config-logging.html |
| postgres_do_not_use_standard_port | 2 | Using the standard port makes it easier for intruders to scan for the service from the outside Remediation: Set the parameter port to any other value than 5432 |
| postgres_log_timezone_utc | 2 | Working in different timezones is a great area of error. For logging, it is generally recommended to use UTC time, and convert in visual tools to local times as needed. By default, Postgres uses the operating system's timezone setting as its timezone for logging. It is best to set it to UTC to avoid confusion, or to your organization's standard time zone setting. Remediation: Set the parameter log_timezone to UTCSource: https://www.postgresql.org/docs/10/runtime-config-logging.html |
| postgres_log_statement_not_none | 2 | By default, log statements are not logged at all. It is useful for auditing purposes to at least set it to ddl, meaning that DROP, ALTER and CREATE statements are being logged.Remediation: Set the parameter log_statement to anything other but none (default value is none).Source: https://www.postgresql.org/docs/10/runtime-config-logging.html |
| dockerfile_container_healthcheck_parameter | 2 | Dockerfiles have an instruction called HEALTHCHECK. It enables a user to define a command to figure out if the program(s) running inside the container are working properly. It is generally advisable to have healthchecks in place to assist monitoring of running containers. Remediation: Have at least one HEALTHCHECK instruction in your Dockerfile.Source: https://docs.docker.com/engine/reference/builder/#healthcheck |
| mysql_do_not_use_standard_port | 2 | Using the standard port makes it easier for intruders to scan for the service from the outside Remediation: Set the parameter port under mysqld to any other value than 3306 (default)Source: https://dev.mysql.com/doc/refman/8.0/en/server-options.html#option_mysqld_port |
| dockerfile_env_and_arg_defined_and_right_away_used | 1 | When creating Docker images that use environment variables or build arguments, it is advisable to position the ARG or ENV directives close to their actual uses, since otherwise the caching for building the images is not greatly used.Remediation: Every variable defined by an ENV or ARG directive should be used within the next five commands inside the Dockerfile. |
| dockerfile_only_one_definition_per_env_statement | 1 | The ENV statement allows multiple definitions. This should be avoided for readability reasons, as well as pitfalls like variables not being evaluated if defined within the same ENV directive. Remediation: Ensure that every ENV directive has only one assignment. |
| dockerfile_do_not_use_add | 1 | Dockerfiles have two directives that allow you to add files from the machine where you build the image into the image, namely COPY and ADD. Both are technically similar, but ADD also has side-effects like automated decompression of archives. It is generally recommended to only use COPY Remediation: Remove any ADD directive in your dockerfile and replace it with COPY.Source: https://docs.docker.com/engine/reference/builder/#copy |
| mysql_enable_slow_query_log | 1 | MySql has a neat feature to log slow queries, which then can be tracked to prioritize optimization efforts. Remediation: Set slow_query_log to the value ON in the configuration.Source: https://dev.mysql.com/doc/refman/8.0/en/server-system-variables.html#sysvar_slow_query_log |
Scan performed at 2022-12-12 15:23:07 using the CoGuard CLI